To support Inde customers throughout 2023's Cyber Smart Week we will be publishing a blog post each day that details a category of mitigation that you can implement to harden yourself against popular adversary techniques. These blogs are to help technical managers and practitioners get a better grasp on how to manage security risks within their business. Our selection is based upon our practical experience in responding to incidents, researching threat actors and adversary simulation engagements.
Today we'll discuss Patching.
Why Patch?
Alongside detection and response capability, the management of software vulnerabilities through patching is widely considered to be the most effective mitigation against device compromise. While software vendors may release updates to fix performance bugs or introduce additional features, they frequently address vulnerabilities which may be exploited by adversaries to achieve a variety of objectives. Some recent examples include:
- Remote code execution:
- Due to their use of an outdated third-party dependency (Apache Santuario), CVE-2022-47966 is a pre-authentication remote code execution vulnerability affecting multiple Zoho ManageEngine products. Exploitation of this initially involved deployment of a webshell which was used to execute reconnaissance commands and download additional tooling. Observed behaviours diversified following release of a public proof-of-concept approximately two weeks after initial recording of the CVE. Reference.
- CVE-2022-41080 (Privilege Escalation) and CVE-2022-41040 (Server-Side Request Forgery), together known as "ProxyNotShell", are vulnerabilities that both affect Microsoft Exchange Server. When chained together, they can be exploited to execute arbitrary PowerShell and thus compromise a target server. These were widely exploited by ransomware actors, such as Play, to serve as an initial access vector into organisations. Reference.
- Privilege escalation: CVE-2023-20198 affects Cisco IOS XE, allowing a remote, unauthenticated actor to create a privilege 15 account on the device. This account privilege allows actors complete control of the Cisco device. Exploitation of the vulnerability has been used to aid deployment of Lua-based implants to upwards of 50,000 devices worldwide. Reference.
- Information disclosure: CVE-2023-4966 is a buffer overflow vulnerability that affects Citrix ADC. It is currently under active exploitation and is reported to have led to session hijacking of accounts that had authenticated against the appliance. Reference.
- SQL Injection: CVE-2023-34362 is a SQL injection vulnerability affecting Progress MOVEit Transfer, permitting the execution of arbitrary SQL queries. Broad exploitation of this was carried out by Cl0p gang, leading to the theft of hundreds of databases and subsequent extortion demands. Reference.
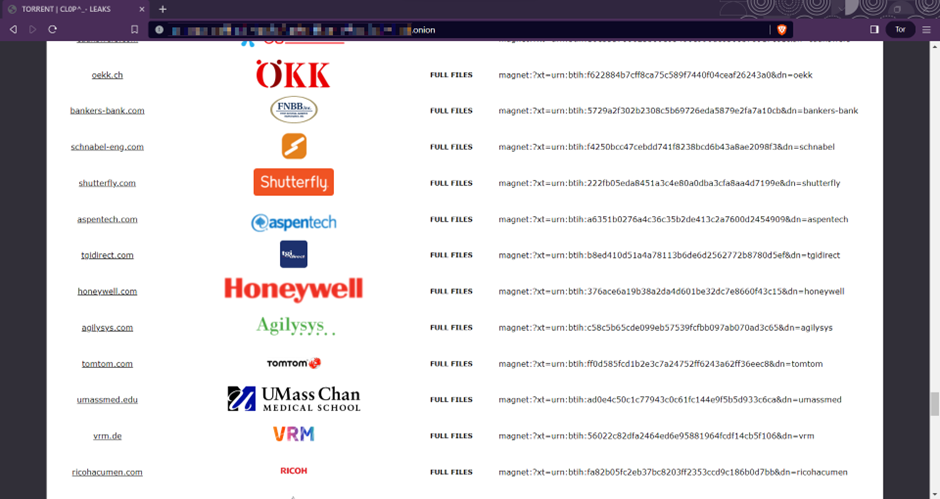
Cl0p leaks following the MOVEit campaign.
Patching Guidance
Above all, it must be ensured that patching is completed in a timely manner. An adversary who has the capability to exploit a given vulnerability does not care about your patch cycle, change control process, nor your uptime requirements. Our general recommendations are:
- Workstations and development-tier servers should receive and install all updates as soon as they’re released. A reboot should be required within 24 hours of installation.
- QA and UAT should receive patches within 24 hours of successful deployment to development.
- Production servers must receive all patches within seven days of release.
- Critical patches should be deployed to all applicable hosts within:
- 48 hours if no exploit is available.
- 24 hours if an exploit or proof-of-concept is available.
If patching follows release of an exploit, compromise assessment should also be undertaken, and it considered whether the act of patching may destroy forensic evidence. Any evidence should first be preserved through memory capture and filesystem imaging.
Early Bird Gets Avoids the Worm
While it may not always be practical and sensible to be on the bleeding edge of new software releases, it is still important to ensure your organisation is prepared to deploy security patches both accurately and promptly. Meeting these targets in most IT environments will require the use of automation for the two key phases of patching:
- Discovery: You can't patch what you don't know about. Depending on the complexity of your software deployment, IT Asset Management (e.g. LanSweeper, NinjaOne), basic Vulnerability Management (e.g. CrowdStrike Spotlight, Defender for Endpoint) or more comprehensive tooling (e.g. Rapid7, Tenable, Qualys) will be necessitated.
- Remediation: In modern environments, there should be very few scenarios where manual patching is needed. Consider using products such as Azure Patch Management and Patch My PC to automate deployment of OS and third-party software patches.
Edge Cases
In some circumstances, particularly in the OT space, uptime or 3rd party support requirements may necessitate deferring or completely avoiding patching. Such systems should be treated as high-risk hardware appliances, and compensating controls applied. This may include:
- Network segmentation.
- Software allowlisting.
-
Policy hardening.
Further Reading